Building services
Heating, Ventilation and Air Conditioning (HVAC) systems are used in many modern buildings to maintain an appropriate indoor environment, for example supplying fresh air to building occupants or cooling to sensitive equipment. The HVAC systems will be controlled by a Building Automation and Control System (BACS), and jointly these systems may also play an important role in incident response procedures such as a smoke and fumes dispersal in the event of a fire.
HVAC systems may act as a potential vulnerability in terms of contaminant (e.g. Chemical, Biological, Radiological or Nuclear (CBRN) material) ingress, spread and subsequent exposure to building occupants. Therefore when designing HVAC systems, the following should be considered:
- Placement and security of HVAC intakes and exhausts
- The security of the BACS, including any connections to systems outside of the building
- Zoning the interior of the building to isolate critical areas
- Understanding who can access and control the HVAC system and BACS (and where they can access or control it from)
- Whether there is a requirement for specialist filtration
- Consideration of how HVAC systems and BACS may feature in, or impact upon, the response to an incident and how this may be different depending on the nature of the incident.
Further guidance on the security of BACS is available here.
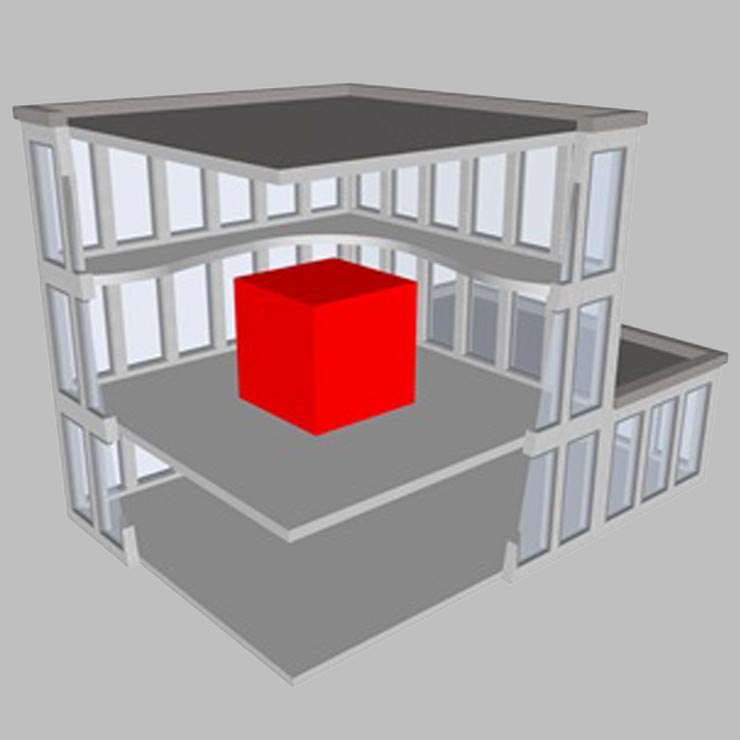
Internal spaces
The majority of internal spcaes in a typical building will be general office, catering or storage space. Access control may be used to limit access to / flow through these areas. Certain spaces, however, may require additional security treatment. These include, but are not necessarily limited to:
- Protected spaces. These are areas into which staff can retreat in case of attack or some other types of incident
- Secure rooms. Typically locations containing sensitive material or equipment with a requirement for limited access
- Secure working areas. These are likely to be areas where sensitive work is carried out and access needs to be tightly limited to authorised personnel
- Armouries (if present)
- Secure equipment rooms
- Security control rooms
When designing such spaces it is important to understand the threats and risks they are being designed to withstand. This will allow the identification of proportionate requirements for:
- Door systems
- Glazing systems
- Obscuration
- Security walling
- Reinforced floors and ceilings
- Electronic security systems
Utilities
It is also important to consider the security of other services and utilities within a building. In particular, the water supply may be a potential vulnerability in terms of contamination. Requirements for security measures should include protection of utilities and consideration should be given to restricting access to authorised personnel only.